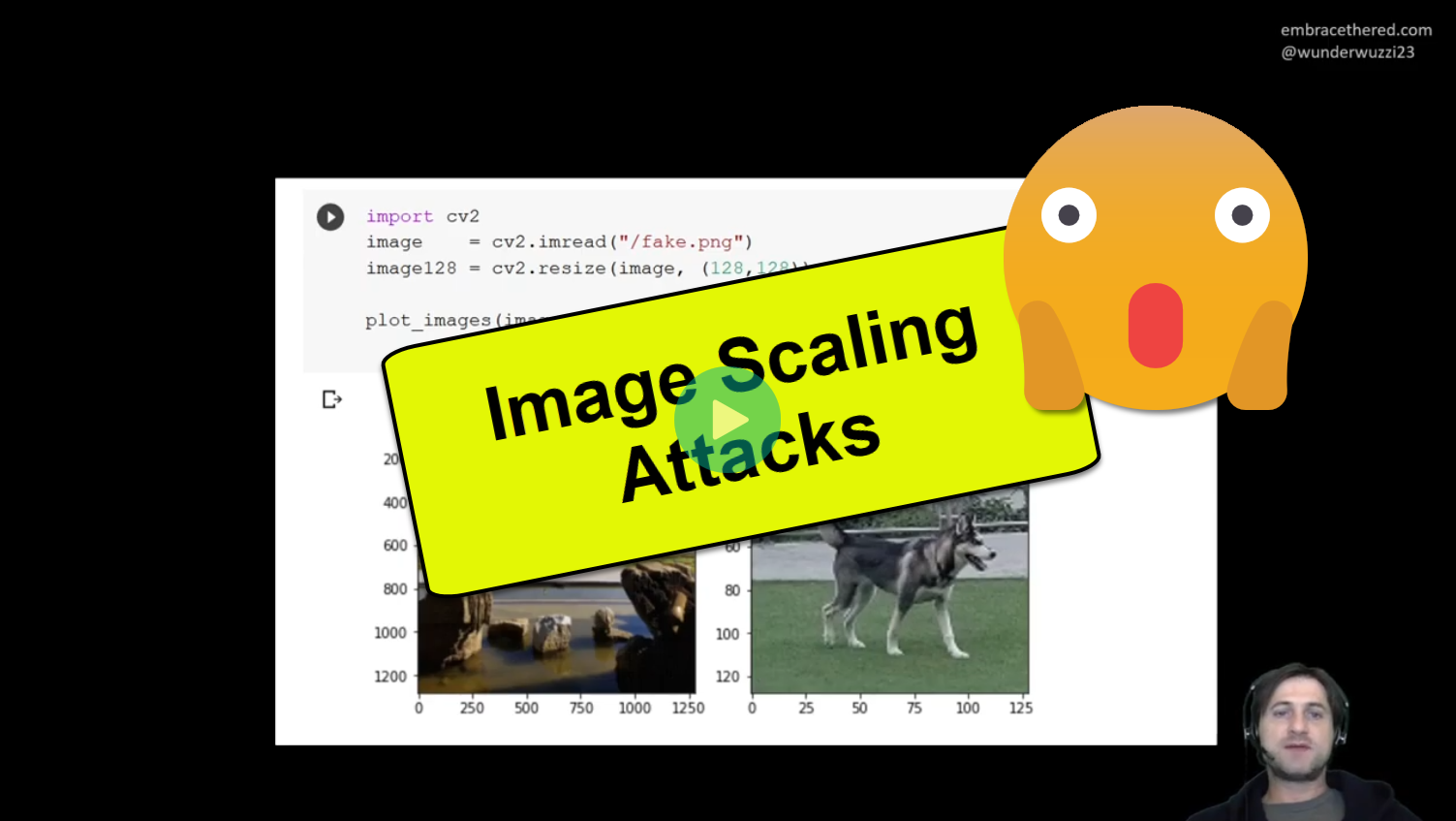
Video: Understanding Image Scaling Attacks
Today you are in for a special treat. Did you know that an adversary can hide a smaller image within a larger one?
This video demonstrates how a small image becomes magically visible when the computer resizes the large image, and also how to mitigate the vulnerability.
This is possible when vulnerable code uses insecure interpolation.
If you like this one check out the overall Machine Learning Attack Series.
Credit for original research, Erwing Quiring, et al., TU Braunschweig.
Stay cool and happy hacking!